Get the audited compiler
Covenant V0.6 GA ships a full toolchain: compiler, CLI, LSP, and VS Code extension. One command to start.
# one command
cargo install covenant-cli
# install cargo install covenant-cli # verify covenant --version # Covenant V0.6.0 (OMEGA V4 audited)
# marketplace kairos-lab.covenant-lang # or via CLI code --install-extension \ kairos-lab.covenant-lang
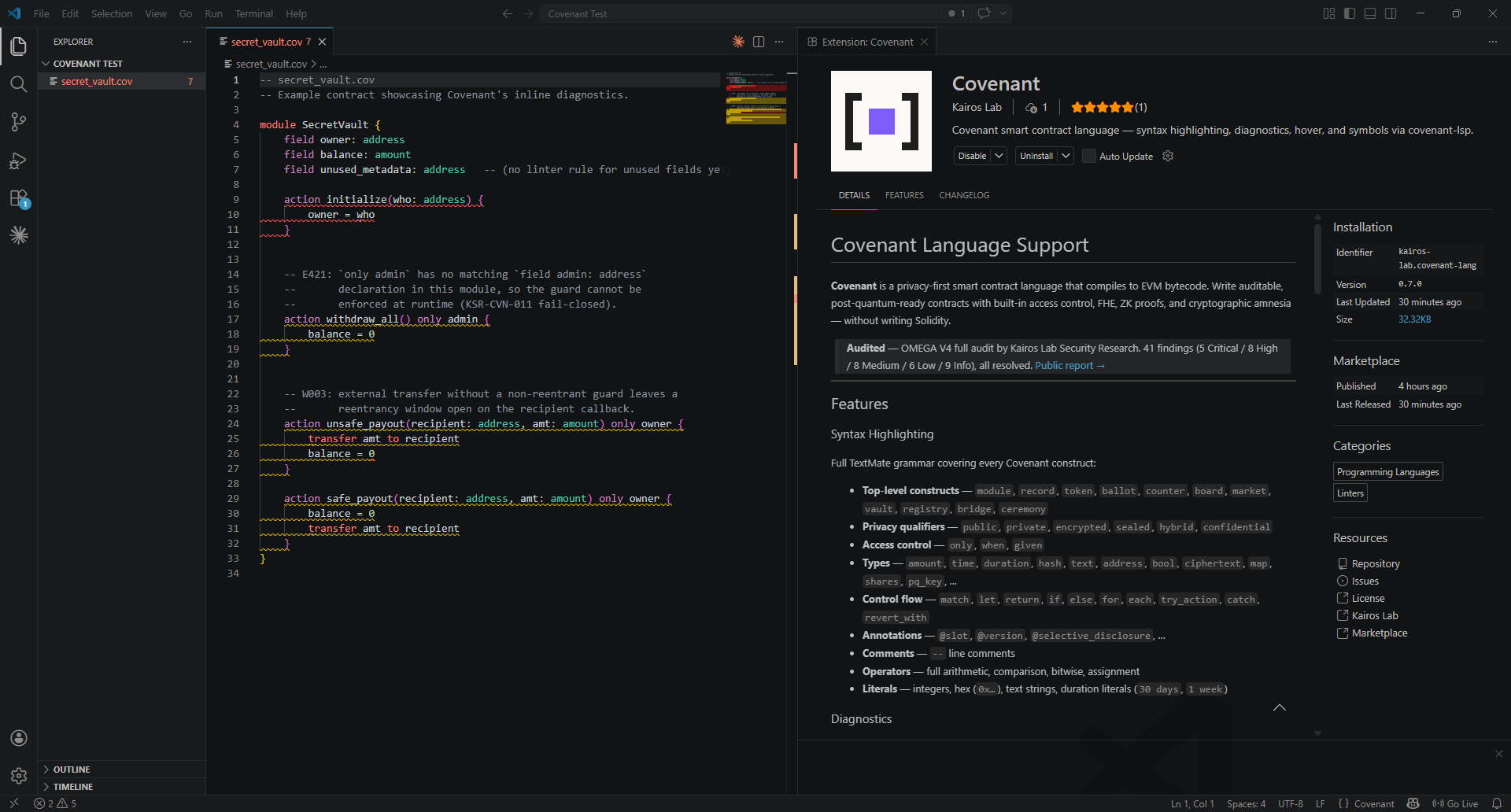
Inline diagnostics in action — E421 (no matching field admin), W003 (reentrancy window) — caught at edit time, not at audit time.